Continuing from the previous post Penetration Testing Your Web App with Azure Application Gateway WAF Part 2: OWASP ZAP Tool, I will show how to query the WAF logs using Azure Log Analytics as it provides near real-time monitoring. To get a more comprehensive implementation of Log Analytics you can read my other blog series on Monitoring Virtual Machines with Azure Log Analytics
In order to setup monitoring, the Azure application gateway’s diagnostics logs have be connected to your log analytics workspace as shown.
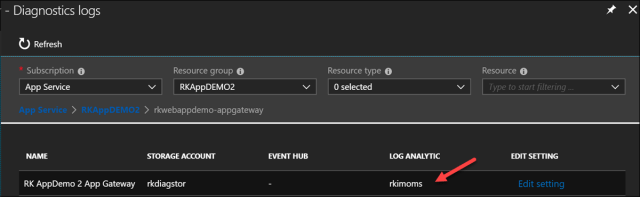
By clicking Edit setting, it was setup with the following check boxes filled and selecting my existing log analytics workspace named rkimoms
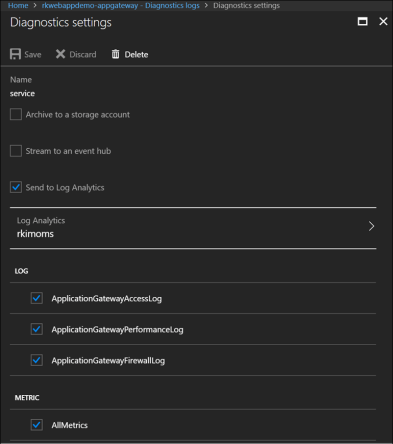
The Send to log Analytics is checked off along with selecting my log analytics workspace called rkimoms.
Going to my log analytics workspace query editor

I execute the following log analytics query to see which requests were detected and blocked by the WAF.
AzureDiagnostics
| where Category == “ApplicationGatewayFirewallLog” and action_s == “Blocked”
| summarize any(details_data_s) by details_file_s, details_message_s, details_data_s, bin(TimeGenerated, 10m)
The query returns the following result

As indicated by the red arrow, you can see 44 detected attacks of the SQL Injection Attack Detected via libinjection rule and where by the OWASP ZAP tool ran this type of attack.
To visualize with a bar chart, I execute a query
AzureDiagnostics
| where Category == “ApplicationGatewayFirewallLog” and action_s == “Blocked”
| summarize count(details_message_s) by details_message_s, bin(TimeGenerated, 5m)
| render barchart
And receive the result

This shows ZAP tool attack scans that I have run several times in a 30 minute period. The bar chart groups the results in 5 min time buckets and by attack detected rule.
So, whether in testing or in production scenarios, use Log Analytics to monitor the web application firewall logs to assess threats.
Resources
Thanks for a very good article series!
I got syntax errors with queries and had to put “| where action_s ==” Blocked “” on seperate line and include ResourceProvider == “MICROSOFT.NETWORK” like this:
AzureDiagnostics
| where ResourceProvider == “MICROSOFT.NETWORK” and Category == “ApplicationGatewayFirewallLog”
| where action_s == “Blocked”
| summarize count(details_message_s) by details_message_s, bin(TimeGenerated, 5m)
| render barchart
There is likely something in my setup, but would leave a comment anyway 🙂
Regards
Bjorn
Hi Bjorn, what is the syntax error? I don’t put two where clauses.