Blog Series:
- Azure AD Application Proxy with a Claims Aware Web App – Part 1
- Azure AD Application Proxy with a Claims Aware Web App – Part 2
- Azure AD Application Proxy with a Claims Aware Web App – Part 3
- Azure AD Application Proxy with a Claims Aware Web App – Part 4
- Azure AD Application Proxy with a Claims Aware Web App – Part 5
- Azure AD Application Proxy with a Claims Aware Web App – Part 6
Objective: Add Azure AD user and demonstrate Microsoft Access Panel
Add Users into Azure AD Directory
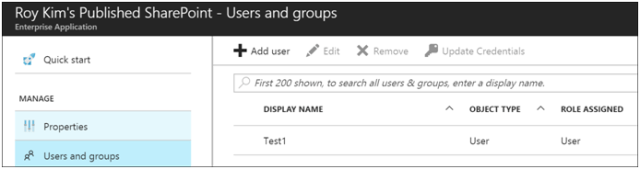
Adding a user to this application for access, I added an existing user Test1 in my SPB2B AD Directory to this application.
Go to the Enterprise Application > Users and Groups
User Test Case
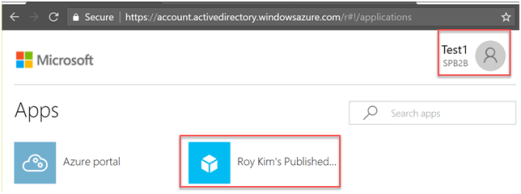
To access the SharePoint app you can either go through the My Apps portal at https://myapps.microsoft.com or go directly to the published SharePoint app URL at https://roykimspublishedsharepoint-spb2b.msappproxy.net/. Either way, you will be first prompted for Azure AD credentials. In this case, the username is test1@spb2b.onmicrosoft.com.
My Apps portal:
For the published SharePoint application, you will be prompted again for any login credentials of the domain user account. At this point in the configuration, there is no single sign-on with Azure AD login.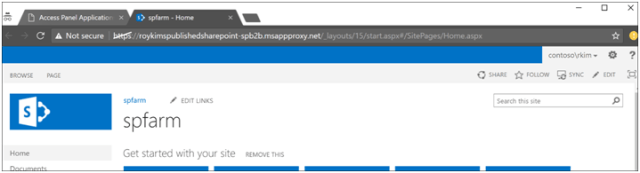
To recap:
- Logged into My Apps Portal such that user was authenticated against Azure AD as test1@spb2b.onmicrosoft.com
- When you click the SharePoint app URL, you will get prompted for credentials that are only on-premise AD domain account credentials. This is not a desirable user experience.
- To solve this problem, one way is to setup single sign-on with Kerberos constrained delegation with Azure App Proxy and Azure AD Connect. This is will be discussed in the next blog.
Pingback: Azure AD Azure Application Proxy with SharePoint Server 2013/2016 Blog Part 5 – Roy Kim on SharePoint, Azure, BI, Office 365
Pingback: Azure AD Azure Application Proxy with SharePoint Server 2013/2016 Blog Part 6 – Roy Kim on SharePoint, Azure, BI, Office 365
Pingback: Azure AD Azure Application Proxy with SharePoint Server 2013/2016 Blog Part 3 – Roy Kim on SharePoint, Azure, BI, Office 365
Pingback: Azure AD Azure Application Proxy with SharePoint Server 2013/2016 Blog Part 1 – Roy Kim on SharePoint, Azure, BI, Office 365
Pingback: Azure AD Azure Application Proxy with SharePoint Server 2013/2016 Blog Part 2 – Roy Kim on SharePoint, Azure, BI, Office 365