Part: 2 Site to Site VPN Connection
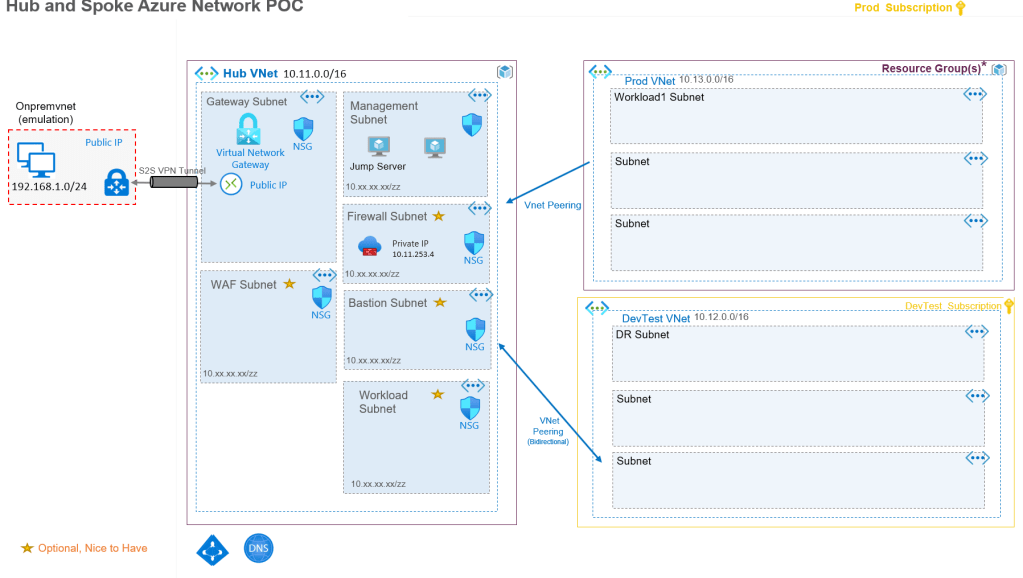
Scenario: Building a demo or proof of concept to understand the technology, azure resources and configuration settings that involve Azure Virtual Networks, VNet Peerings, Virtual Network Gateway, and Site to Site VPN Connections. The architecture is to emulate a hybrid cloud topology with on-premises network emulated with an Azure VNETs in a hub and spoke network topology.
My Azure CLI script to build most of this network architecture can be found at https://github.com/RoyKimYYZ/azurehubandspokenetworkpoc/blob/main/create-hubandspokenetwork.azcli
Site to Site VPN Connection Design
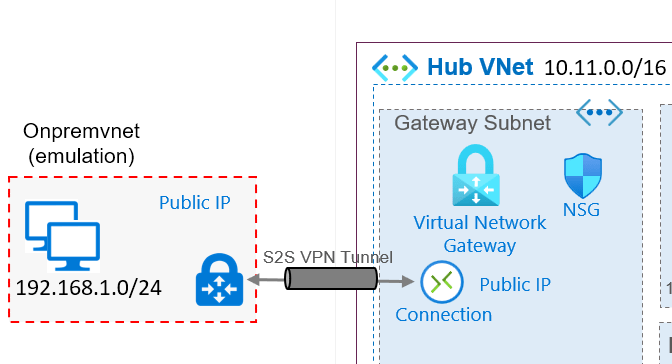
In this architecture I am laying out an “on-premises VNET” that is emulating an on-premises network or even any another other Cloud Network such as AWS or GCP or even another Azure virtual network in a different organization. A site 2 site VPN is a relatively easy, fast and cheaper option over an Express Route Connection.
This VPN connection is the construct for enabling a hybrid cloud architecture.
“A Site-to-Site (S2S) VPN gateway connection is a connection over IPsec/IKE (IKEv1 or IKEv2) VPN tunnel. S2S connections can be used for cross-premises and hybrid configurations. A S2S connection requires a VPN device located on-premises that has a public IP address assigned to it.”
The on-premises virtual network gateway represents on on-premises network vpn device. The Hub VNet requires a gateway subnet for the Virtual Network Gateway. Also there requires a public IP address for the VNET Gateway to facilitate a VPN connection between the networks.
A site to site VPN is a good starting point and can have an a more enterprise grade Express Route connection as part of a future road map. For an on-premises network, there would be a VPN device that the Azure Virtual Network Gateway need to establish a connection. There typically a public IP address on both sides. To read about VPN devices that an Azure virtual network gateway can connect to refer to https://docs.microsoft.com/en-us/azure/vpn-gateway/vpn-gateway-about-vpn-devices
For a virtual network gateway in the hub VNet, must be placed in a gateway subnet.
A connection needs to be created to establish the site to site VPN connection. This is added in the virtual network gateway in the hub VNet. A shared key is used to establish the VPN connection between the virtual network gateways in this design.
Read further for the Hub and Spoke VNET design in part 3.

Pingback: Building a Hub and Spoke Azure Network with Site to Site VPN Part 1 Architecture – Roy Kim on Azure, Office 365 and SharePoint