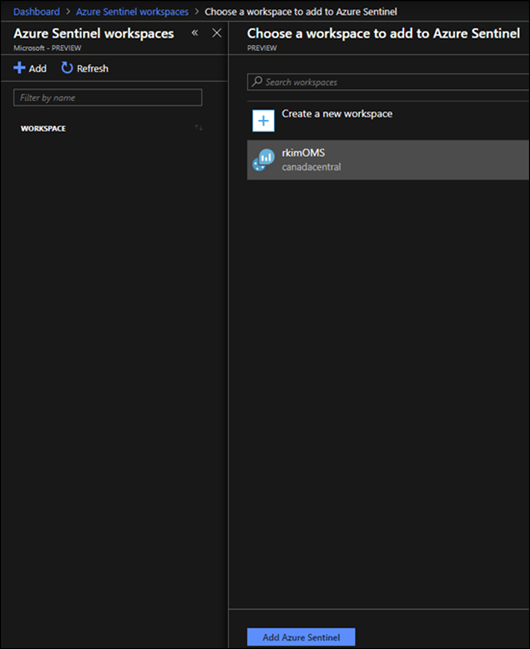
Continuing from the previous post Part 1, Let’s setup Azure Sentinel with a Log Analytics Workspace.
To setup Azure Sentinel, you need to add a log analytics workspace. In my case, I have an existing log analytics workspace, called rkimOMS, that is already configured to collect diagnostic data from an existing application gateway.
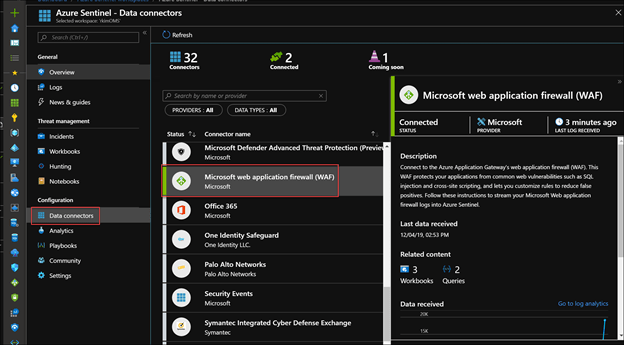
Data Connectors
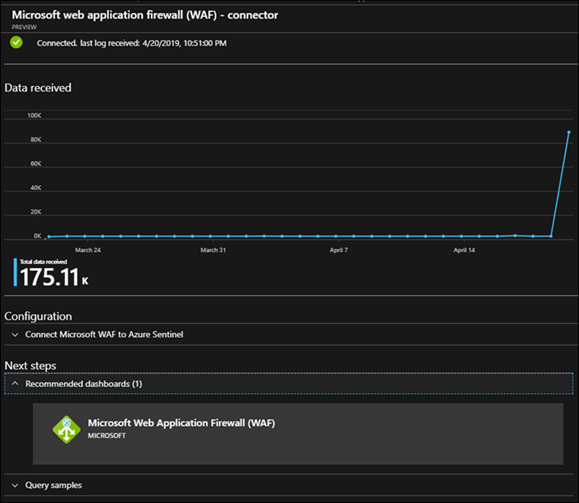
Next, Connect Azure Application Gateway’s web application firewall (WAF) as a data source.
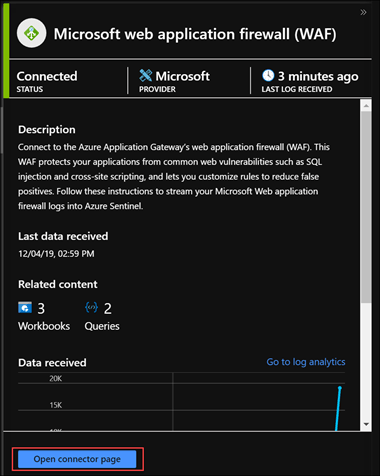
Open Connector page
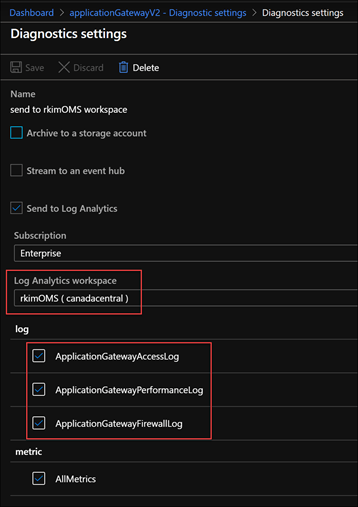
Remember that the existing App Gateway needs to have its diagnostics setting to send logs to the log analytics workspace added to Azure Sentinel. You can do this manually at the App Gateway resource diagnostic settings.
Here we can see some data received via this connector to validate it is setup appropriately.
Now Azure Sentinel is setup to work with the Azure Application Gateway Web Application Firewall.

To continue reading, click for Part 3 – Monitoring of web attacks

Pingback: Using Azure Sentinel with Azure App Gateway to Investigate Web Attacks – Part 1 Intro – Roy Kim on Azure, Office 365 and SharePoint
Pingback: Using Azure Sentinel with Azure App Gateway to Investigate Web Attacks – Part 3 Monitoring – Roy Kim on Azure, Office 365 and SharePoint