Azure Bastion provides remote desktop or SSH access to Azure Virtual machines that are private within the network.
I work with bastions or what I call jump servers to manage Azure IaaS resources quite often and so excited to hear about Azure Bastion as a PaaS offering.
A Typical Scenario
In a secure public cloud environment of IaaS infrastructure, it is common to RDP or SSH into a VM in a remote access scenario so that a system admin can then access or manage internal and private Azure resources such as VMs.
The added effort in setting up a VM jump server are security hardening, networking, access, patching and more. So why not take this scenario and provide a technology solution delivered as a cloud managed service – Azure Bastion!
Azure Bastion Features and Benefits
- RDP and SSH directly in Azure portal – Via a browser for convenience and portability
- Remote Session over SSL and firewall traversal for RDP/SSH – firewall friendly
- No Public IP required on the Azure VM
- No hassle of managing NSGs – convenience
- Protection again port scanning
- Protect against zero-day exploits. Hardening in one place only – Secured.
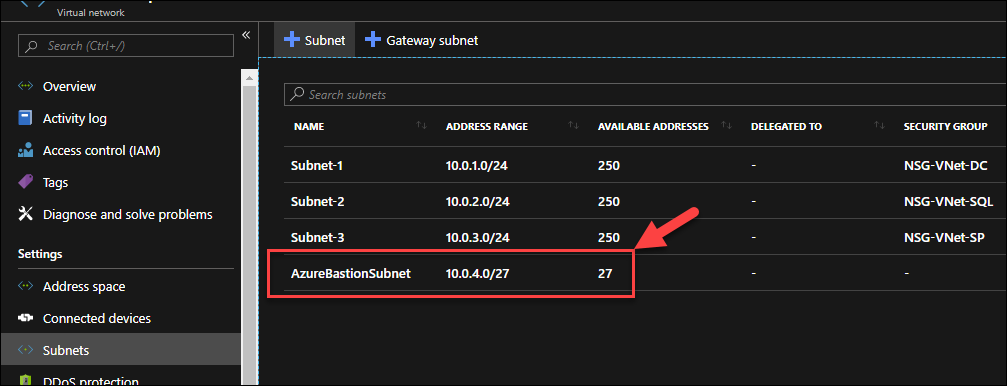
Prerequisites – For an existing VNET, it has to be located in the currently supported regions (East US, West US, West Europe, ..) for this preview. You must add a subnet with name AzureBastionSubnet with a prefix of at least /27
Run the following. In my case, I am using the Az PowerShell module
Get-AzSubscription
$subId = ''
Select-AzSubscription -Subscription $subId
Register-AzProviderFeature -FeatureName AllowBastionHost -ProviderNamespace Microsoft.Network
Register-AzResourceProvider -ProviderNamespace Microsoft.Network
Get-AzProviderFeature -ProviderNamespace Microsoft.Network
Get-AzProviderFeature
Note that registering the feature took me about 20 minutes.
You must use this link http://aka.ms/BastionHost to access the Azure Portal that allows the use of this new preview features.
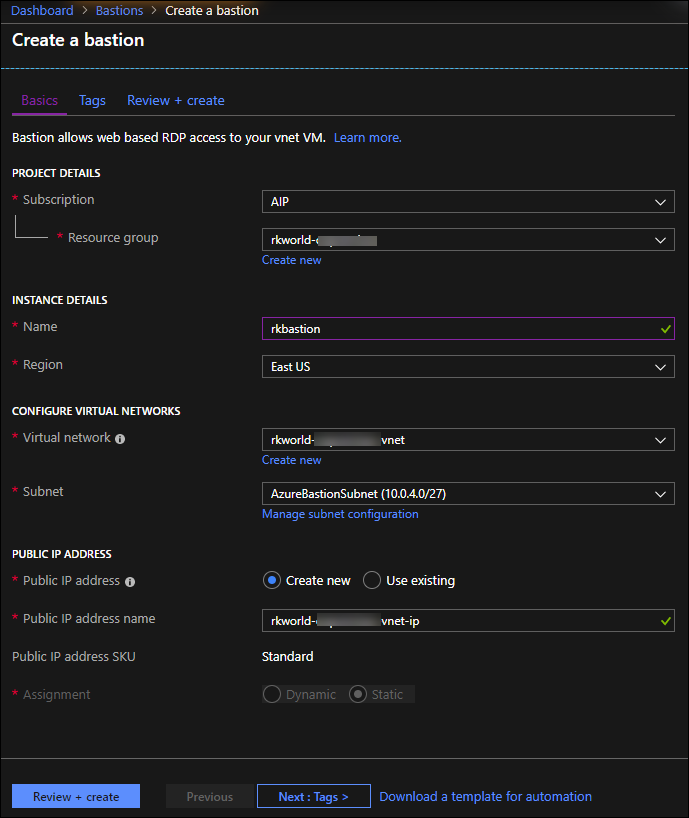
Find the Azure Bastion service and click Create
Note that you must select AzureBastionSubnet that was just created.
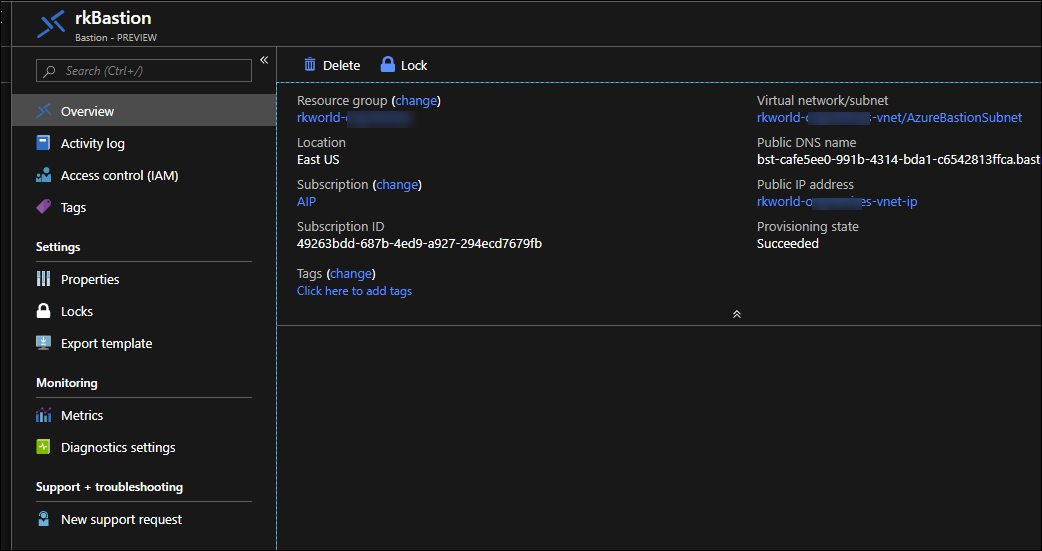
Upon deployment, the overview blade looks as follows. Note that you can’t connect to a VM through this blade. There is nothing functional here.
Go to the Azure VM and click on Connect as you normally would
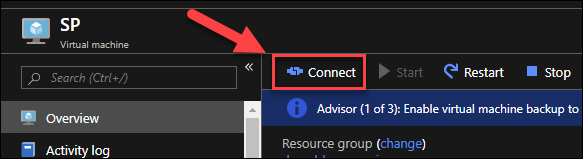
You will see a new 3rd option to connect

Click Connect
In connecting to this windows VM, you will see a remote desktop window in the browser.
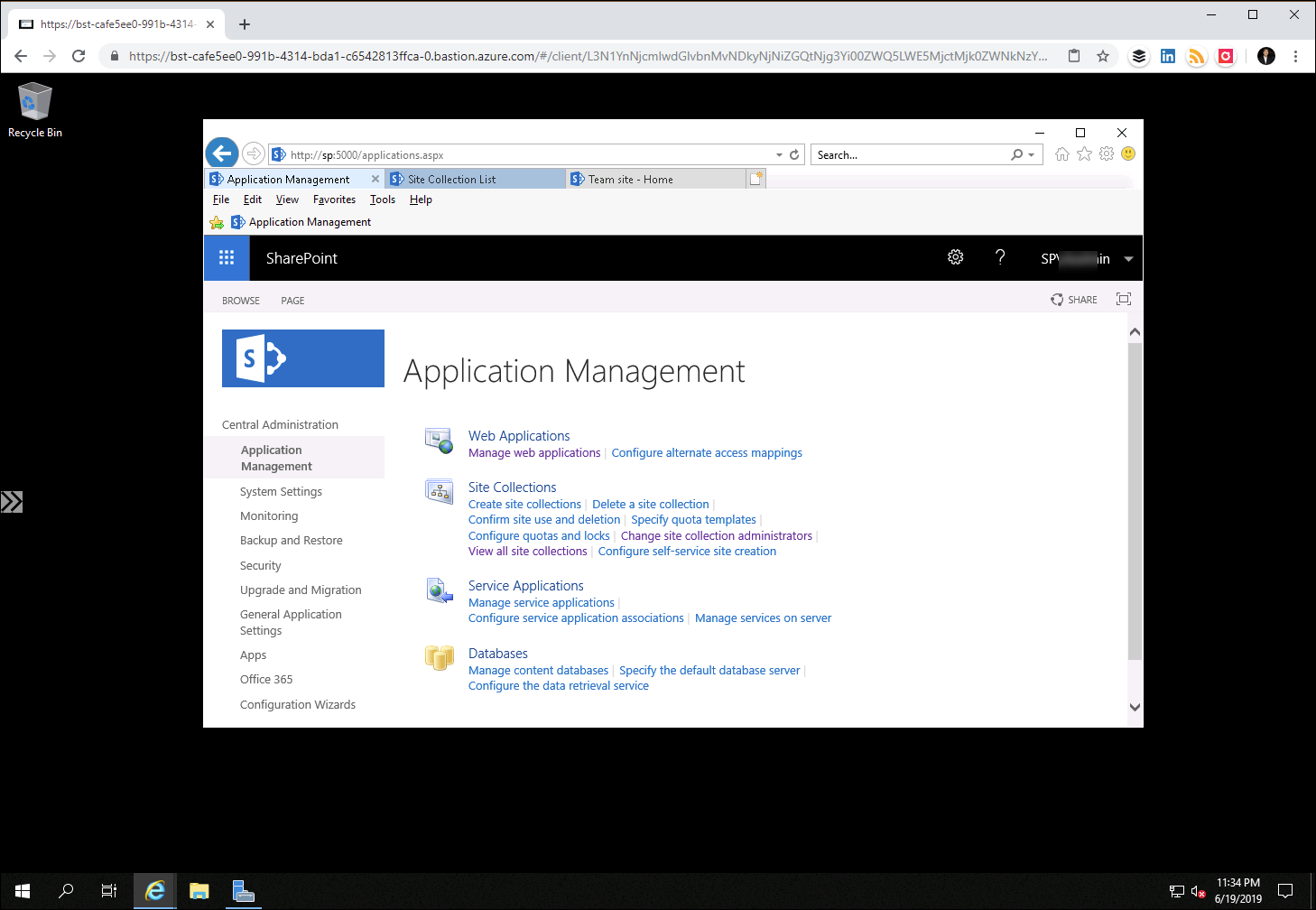
And so you can manage your VMs. In this case, I am accessing a SharePoint Server VM.
Commentary
I feel this new service has a lot of promise for small medium business and small enterprise where they may not have a rigorous virtual data center model. For example, some large enterprise won’t even allow public remote access to the azure portal and so you can’t even get to the bastion service via Azure Portal. I’m excited how this new service matures as I see it as a common pattern in an azure architecture of private resources.
For Azure Bastion roadmap items, there is mention in the comments at the bottom of the article. I have compiled a list of some of them:
- Remote App Streaming with Azure Bastion
- Support for AAD, web experience available behind a AAD 2FA
- Support for auto-scale
- Support for SQL Managed Instance and SQL SSMS
- Using native client application support so that you can use your existing RDP/SSH client applications
- Using RDP routed through Express Route/S2S VPN
- Proxy-ing through the bastion host
- Integrate with other Azure Resources like VMSS
- VNet peering
Online References
For detailed reading and source information of this blog.
- Announcing The Preview of Microsoft Azure Bastion
- Create an Azure Bastion host (Preview)
- Azure Bastion Key Features
- Azure Bastion FAQ (Preview)