Scenario: The SSL certificate used in my Azure Application Gateway has expired and needs to be replaced. This SSL certificate was bought through the Azure Portal.

Background:
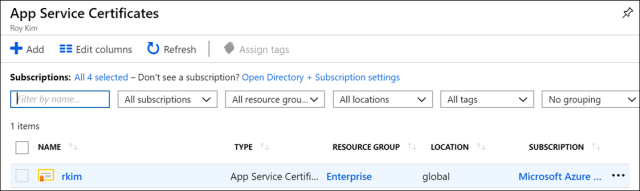
- The certificate was provisioned through the App Service Certificate service in Azure.
 The certificate is store in my Azure Key Vault.
The certificate is store in my Azure Key Vault. - The App Gateway is used as an application delivery controller for my azure web app. The certificate is referenced through one of the Http Listeners.
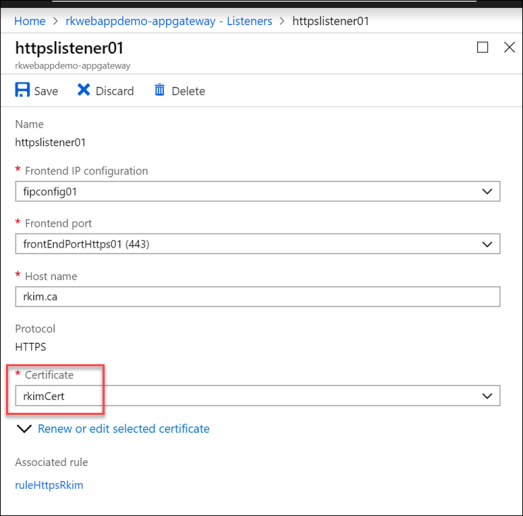
To simply renew or replace the expired certificate, simply click as follows, but where and how to get your renewed certificate?

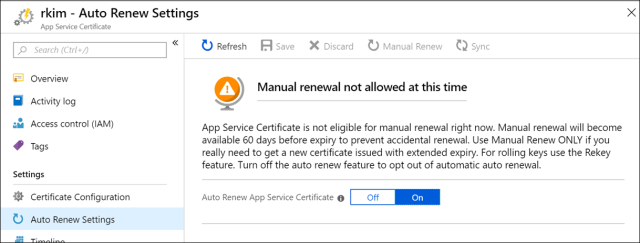
For further background, my certificate was set to auto renew.
And my certificate was also imported to my Azure key vault via the certificate configuration.
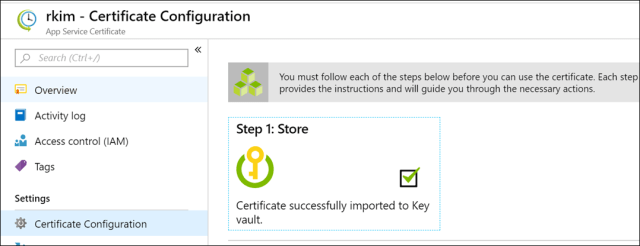
Clicking into “Step 1: Store”

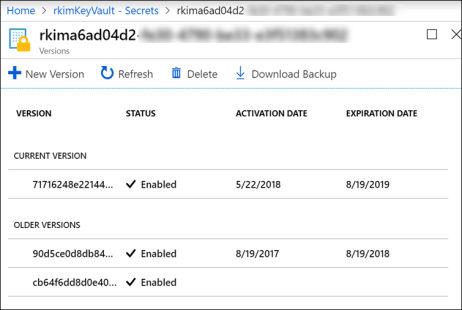
Going to my key vault, my certificate is in the Secrets blade

As you can see the certificate was already renewed with a new expiration date of 8/19/2019 by one year.
Clicking into the certificate for more details.
So where and how to get this certificate?
Go back to App Service Certificate service and click on Export Certificate. Click the Learn more link for further instructions.

This link leads to a Microsoft blog article title Creating a local PFX copy of App Service Certificate providing a PowerShell script to export the certificate to use in other Azure resources such as the App Gateway. So there really is no ability as you may expect to export through the Azure portal.
From this article, I simplified the script for myself as follows by simply providing my key vault name and name of the secret. You can choose this option if it serves you well.
$secret = Get-AzureKeyVaultSecret -VaultName rkimKeyVault -Name rkima6ad04d2-fe30-4790-be33-e3f51394c999
$pfxCertObject= New-Object System.Security.Cryptography.X509Certificates.X509Certificate2 -ArgumentList @([Convert]::FromBase64String($secret.SecretValueText),"",[System.Security.Cryptography.X509Certificates.X509KeyStorageFlags]::Exportable)
$pfxPassword = -join ((65..90) + (97..122) + (48..57) | Get-Random -Count 50 | % {[char]$_})
$currentDirectory = (Get-Location -PSProvider FileSystem).ProviderPath
[Environment]::CurrentDirectory = (Get-Location -PSProvider FileSystem).ProviderPath
[io.file]::WriteAllBytes(".\appservicecertificate.pfx",$pfxCertObject.Export([System.Security.Cryptography.X509Certificates.X509ContentType]::Pkcs12,$pfxPassword))
# Print the password for the exported certificate
Write-Host "Created an App Service Certificate copy at: $currentDirectory\appservicecertificate.pfx"
Write-Warning "For security reasons, do not store the PFX password. Use it directly from the console as required."
Write-Host "PFX password: $pfxPassword"
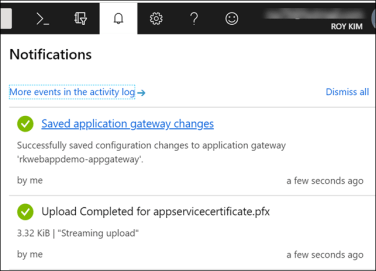
The output:

Go back to your app gateway and then to the Http Listener to renew and upload the exported pfx file and enter the password provided from the PowerShell script output

Click Save
After waiting about 10 minutes to the app gateway successfully updates.
Alternatively, you can renew the certificate with the pfx file with PowerShell here: https://docs.microsoft.com/en-us/azure/application-gateway/renew-certificates#azure-powershell
I test accessing my site again, using Edge browser, and to confirm the site loads properly and the updated certificate expiry date.

Now this process would be much more streamlined if the Http listener can reference the key vault secret. If you go to the following link you can vote for this feature.
Support SSL certificates stored in Key Vault secrets for listeners and backend HTTP settings on Application Gateway
Azure Web Apps support the ability to store an SSL certificate in a Key Vault secret. A certificate resource can be created that references the Key Vault secret. The App service will periodically check for an updated SSL certificate in the Key Vault. The Application Gateway needs to have the same support for storing the SSL certificates in the Key Vault. It should be able to reference a Key Vault secret that contains the SSL certificate in the listener and backend HTTP settings configuration. This capability will allow the management of SSL certificates for Application Gateway and the Web Apps in a single place.
As of this writing (11/27/2018), this feature is planned as stated:
![]()
In conclusion, I have demonstrated how to update an expired certificate in an Azure resource. As you can see, sometimes such activities aren’t as straight forward as one would hope and so you have to be equipped with an understanding of Azure PowerShell to do things that the Azure Portal doesn’t support at the time.
Lovved reading this thank you