I have been working with Istio Service Mesh with Azure Kubernetes for a couple years, I like to share my experiences that were beneficial and impactful in my projects.
Istio Service mesh helps with managing traffic among your microservices applications. Read more at https://istio.io/latest/about/service-mesh/
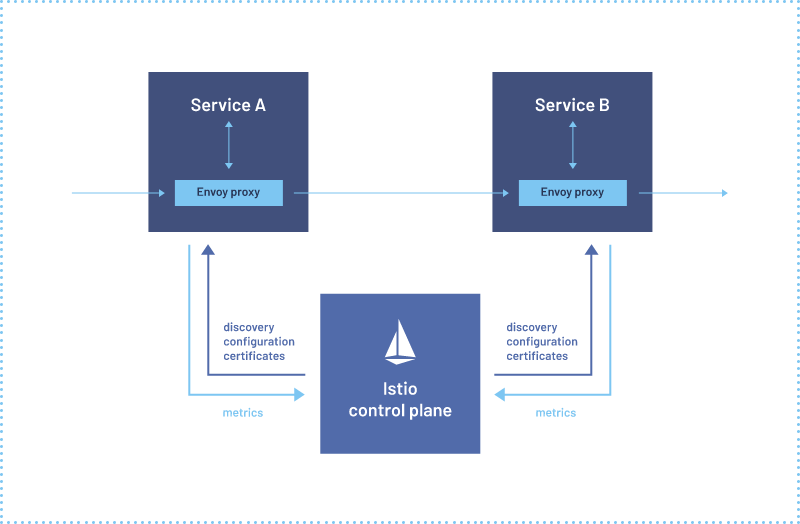
The general architecture is as follows where a service A (in your microservice or distributed application) calls service B. The envoy proxy is a sidecar container hosting the Envoy proxy that assists with traffic management. The Istio control plane manages what is configured in the Envoy proxies.
These are key benefits I have experienced first hand in using Istio Service Mesh into production with Azure Kubernetes Service for microservices application
- Traffic Management for support blue green deployment.
Istio helps with blue green deployments for each of your services. You apply version labels on each of the services such as v1 and v2. And in the Virtual Service YAML file rout the traffic based on rules to the respective version. One can easily go a step further by directing 0 to 100% traffic to the new version and ramp up as you gain confidence in the stability. Further more direct traffic for a subset of users or requests based on http headers. A good example if the a user is using a certain device such as android, ios or windows PC. In the event of an issue with the new version, simply revert traffic back and this can be executed very quickly.
The key benefit is the flexibility, control and ease of management to do such operations. Also that managing this is decoupled from application code and infrastructure or middleware such as the web server. Using Istio with Azure Kubernetes Service is very seamless and there are no nuances or complexities. AKS just serves as a hosting platform for Istio. There are no AKS specific integration features if one is wondering.
3. Observability of the Service Mesh
An important aspect of traffic management of your application service mesh is observability which is basically monitoring your service mess traffic flows, errors, logs and visualization.
Kiali is an open source too that works tightly with Istio and helps with visualizing your service mesh.
Some examples of visualizing are as such:


These visualizations were helpful in project deployments where troubleshooting and health monitoring were necessary.. You can click on a traffic flow edge or node and see the rate of flow, error % and most importantly http status codes. There situations where status codes were 50x errors that lead to look into the application code for troubleshooting. This is also helpful when you are overseeing many applications across many namespaces in an Kubernetes cluster which gives you a birds eye view and drill down for inspection.
From an Azure Kubernetes Service perspective, I complement the use of Kiali with Azure Monitor for Kubernetes. I use this to get metrics on trouble areas. I also use this to cross check and verify if any false positives coming from Kiali.
3. Security with Authorization Policies
With security being a top priority, Istio helps with added layers of security between microservices and distributed applications. Let’s say you have an application in namespace A and another application in namespace B. There is a security requirement that locks down unnecessary traffic between such namespaces or allows specific forms of traffic or http requests. In my project experiences this is where cloud security teams have defined such requirements and Istio would help further support.
For reference, you can read https://istio.io/latest/docs/tasks/security/authorization/authz-http/
From the Istio documentation, this diagram shows a service A authorizes certain requests from workload B. The Envoy proxy contains the configuration and does the work to authorize the traffic requests. All other requests would be denied. And can be the same vice versa from the point of view of workload B.
In my project experience, this is a beneficial approach where managing cross communication security doesn’t have to be hard coded or managed at the application code level, web server or infrastructure level. It adds to the flexibility and manageability of traffic security with Istio.
Conclusion
I have shared 3 key benefits that I can attest were very beneficial in my project experience and recommend to others contemplating and assessing Istio against other service mesh software.


